I’ve played with the stream component before, but not the ISF (Independent Stream Forwarder).
We wanted to ingest netflow data so had to use the ISF.
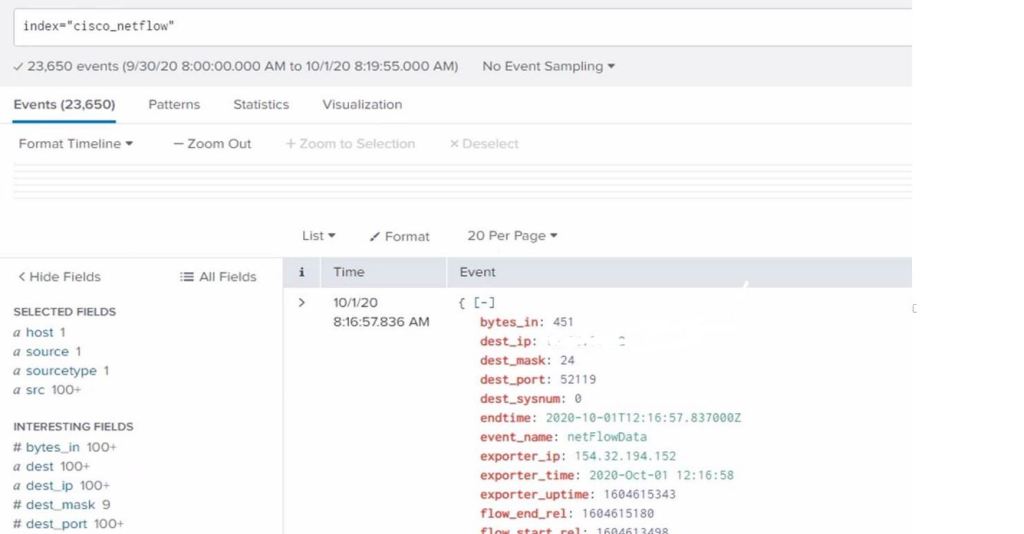
I created an index = cisco_netflow on my test AIO Splunk server
I configured this on a dedicated Linux server. When you install the stream app is creates a HEC point in /opt/splunk/etc/apps/splunk_httpinput/local and you have to enable it before using it.
[http://streamfwd]
disabled = 0
token = ad4c40ab-b234-4a60-b2a5-2a8f61b2f9aa
[http]
disabled = 0
#enableSSL = 0
I checked to see the HEC not to point to a dedicated index, as the ISF sends its own logs to the _internal index, if you set it to a specific index, it will fail.
I configured the Stream App with the config with the ISF would use.
Log in to the search head (AIO) where the Splunk App for Stream is installed.
Navigate to the Splunk App for Stream, then click Configuration > Distributed Forwarder Management.
Click Create New Group.
Enter a name. For example, CISCO_NETFLOW.
Enter a description.
Click Next.
Enter CISCO_NETFLOW as the rule and click Next.
Do not select any options. Click Finish.
Navigate to the Splunk App for Stream, then click Configuration > Configure Streams.
Click New Stream > Metadata.
Enter Name as CISCO_NETFLOW.
Select NetFlow as the protocol.
Selecting NetFlow works for NetFlow, sFlow, jFlow, and IPFIX protocols.
Enter a description then click Next.
Select No in the Aggregation box then click Next.
(Optional) Deselect any fields that do not apply to your use case then click Next.
(Optional) Develop filters to reduce noise from high traffic devices then click Next.
Select the index (cisco_netflow) for this collection and click enable then click Next.
Select only the CISCO_NETFLOW group and Create_Stream.
Configure your NetFlow generator to send records to the new streamfwd.
I then created a distributed forwarder group, used the name of the ISF as a regex match, so the stream app will deploy the config to it.
You then copy the install script command from the app and run it on the ISF server, you then check the streamfwd service and ensure it will restart on a reboot.
sudo service streamfwd start (only manual)
sudo service streamfwd status
sudo systemctl enable streamfwd (on reboot restart)
Run through the OS settings
https://docs.splunk.com/Documentation/StreamApp/7.3.0/DeployStreamApp/Deploymentrequirements
Now check the inputs.conf file, if its not configured then add below with your specs
[streamfwd://streamfwd]
splunk_stream_app_location = http://MY_SPLUNK_SERVER1:8000/en-us/custom/splunk_app_stream/
disabled = 0
Then configure the stream.conf
See the details https://docs.splunk.com/Documentation/StreamApp/7.3.0/DeployStreamApp/streamfwd.conf
Configure the device to send netflow data, if your config is good, you should see data in the index