
There’s a lot of insiders that do a lot of copying and this is one method that could help you observe who’s copying the data when they shouldn’t be init!.
Install the https://splunkbase.splunk.com/app/833/ which is the TA for collecting Linux OS data onto your restricted Linux servers. Once this has been ingested into Splunk, check the sourcetype and ensure the data is correct and the parsing is good.
TA version used there was 5.2.4
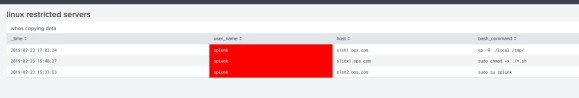
SPL = index=linux sourcetype=bash_history

If the data looks good, create a table, run a simple SPL search to check for any copy or running sudo command for this sourcetype.
SPL = index=linux sourcetype=bash_history sudo OR cp | table _time, user_name, host, bash_command

From this you could enhance the table with some colours and see which user has been a very naughty boy OR girl!!!!
You could do other tables or charts which show data being deleted, which could be a disgruntled employee wanting to do some damage before they leave.
Done!