
Splunk steam once configured can monitor many protocols over the wire, so I wanted to see what I could get into Splunk.
I configured the stream app https://splunkbase.splunk.com/app/1809/ which includes a binary that captures the packets onto a number of test servers running the universal forwarder. In the real world you may use a tap port or use the independent Stream Forwarder which uses HEC, so you could ingest network data straight to it.
My config was on some test servers to capture the packets via the streamfwd binary.
Follow the Stream documentation for the config: https://docs.splunk.com/Documentation/StreamApp/7.1.2/DeployStreamApp/InstallSplunkAppforStream
Also deploy the Stream App onto the search head which provides the dashboards / props /transforms and configuration of the Stream App
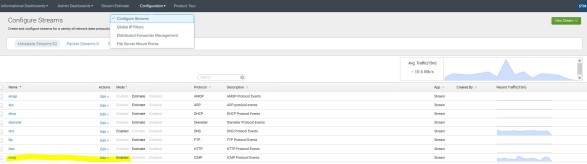
So I wanted a simple check on icmp traffic, so I enabled the icmp protocol in the config in the Stream app Configuration > Configure Streams
I ran some ping checks and could see the data via a basic SPL:
index=dc_stream sourcetype=”stream:icmp” | table src_ip, dest_ip, protocol_stack, bytes, bytes_in, bytes_out

I created a simple chart to see the data and which destination has had most icmp packets
SPL: index=dc_stream sourcetype=”stream:icmp” | timechart sum(bytes) as total_bytes by dest_ip

So this demonstrates how one can capture wire data and then run some SPL to get stats on network traffic your interested in.
Here’s some other stream data dashboards examples that you get.
DNS is a good, you could see how active the DNS server is.
Done.
This app is helpful in getting wiredata into Splunk – go check it out
https://splunkbase.splunk.com/app/4372/